In our previous discussions about design methodologies for IoT devices, we have highlighted the importance of low-power MCUs and secure communication protocols. Now, let's dive into the challenge of uniquely identifying each unit during large-scale production and how fleet provisioning can help.
Traditionally, inputting data into each device individually during production can significantly increase operational costs. To address this challenge, AWS has introduced fleet provisioning as a feature of FreeRTOS, the MCU-installed operating system. Renesas has also developed a reference implementation that integrates this function.
Renesas Reference Implementation
During the final phase of development, we are collaborating with AWS to organize the code on GitHub, ensuring its usability for distribution.
The reference implementation seamlessly functions on standard Renesas boards like the RX72N Envision Kit and the CK-RX65N. Additionally, it can operate on partner-manufactured boards or customer-developed boards using the Smart Configurator.
The Fleet Provisioning function can greatly enhance production efficiency. The following figures illustrate these significant improvements.
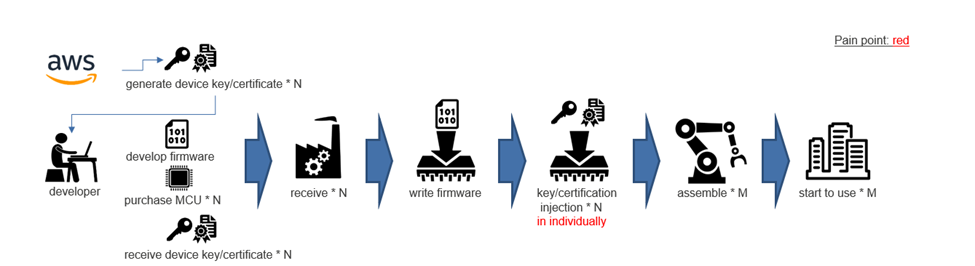
Without Fleet Provisioning
The process of individually injecting keys into N devices is required. This involves injecting unique key data or certificate data for each device one at a time, which puts a significant strain on the production process. Although we can improve production efficiency with a specialized writing process, the design and implementation of this custom procedure would still increase overall costs.
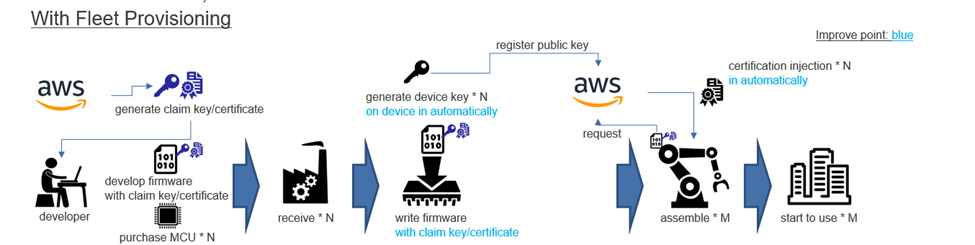
With Fleet Provisioning
There is no need to individually inject keys into N devices. Instead, after the "assemble * M" process in post-production assembly, the devices can use their internet connection to communicate with AWS. Through automated uploading of key data generated from random numbers within the device and downloading certificate data, followed by self-injection, this entire process can be done automatically. It can easily integrate into the traditional firmware writing and product assembly processes, reducing the burden on production and design costs significantly.
We understand that factory production efficiency is a top concern for our customers. Fleet provisioning not only improves production efficiency but also enhances security by eliminating the need to send unique key/certificate information for each device to the factory. The prime benefit of fleet provisioning, from a developer's perspective, is the heightened security it provides.
When examining the mechanisms we have implemented, we have identified a vulnerability in the "assemble * M" process. During this stage, the device communicates with AWS to receive keys/certificates. However, the internally generated keys are stored in readable flash memory, which presents a security risk. To address this, we plan to utilize the Trusted Secure IP integrated into the RX family. This will allow us to generate the key pair within the security IP, minimizing the risk of key exposure outside the MCU. With this solution, the private key will only function within the security IP throughout the product lifecycle.
In addition, the presence of claim keys/certificates embedded in firmware can pose potential risks. However, these can also be safeguarded with the security IP of the RX family. This ensures that confidential information remains secure. Our goal is to provide solutions that enhance production efficiency while guaranteeing complete data protection. By advocating for this approach, we aim to create an environment where end users can trust and confidently use IoT devices.
Lastly, we would like to share links to the RX family's cloud solution, which offers a first-hand experience of these features and a range of security solutions. We hope you find them valuable.