So, you've built an awesome new radio-enabled device that is ready to hit the market, and now you're being asked to prove it is secure and certify it. If you've used a Renesas Bluetooth® device, you're in luck. We've got your back with built-in security features and a full set of tools, guides, and support to make the whole process easier. This post provides insight into what needs to be done and how Renesas enables you throughout this process.
Radio-Enabled Devices: Be Secure and Prove It
When talking about device security, I face different types of reactions: Some consider this a side feature, something they can purchase and simply add to their products. Some see it only as a regulatory burden. Others stress the complexity and the cost it seems to entail. And some, who have been there before, understand that it is just one more must-have feature of their product. A feature that needs expertise and knowledgeable partners to define, develop, and deploy.
Securing your radio-connected devices might seem tricky at first, but it's essential. Here's a simple way to break it down:
- Define Security Goals: Decide on your product's security objectives, including any regulatory requirements (for example, is it in EU compliance with the Radio Equipment Directive - RED and the Cyber Resilience Act - CRA).
- Analyze Gaps: Compare your initial design against these objectives and identify where it falls short—whether in hardware, software, or process.
- Update Design: Adjust your design to close the gaps. Choose hardware and software components that support the new security features, such as secure booting or encrypted communications.
- Document Security Measures: Thoroughly document the implemented security features to ensure traceability and facilitate audits, especially for compliance certification.
- Test Security Features: Perform rigorous testing to validate that all security measures function as intended and can withstand potential threats.
- Protect at Production: Put measures in place so that when the product leaves the developer's bench and moves to production, it is protected from malicious actors.
- Certify and Deploy: Obtain necessary certifications to prove compliance and deploy your secure product with confidence.
Note that achieving security doesn't stop with the initial design and implementation. Consider the risks during development, production, and distribution. For instance, a product could be compromised before it reaches its end users due to insufficient safeguards during manufacturing or transport. Additionally, security concerns extend to the disposal or transfer of the product, particularly if sensitive data remains accessible, posing risks to privacy and confidentiality.
Renesas understands these challenges and offers comprehensive solutions to mitigate them. We provide not only secure devices but also the tools, documentation, and support to safeguard products throughout their lifecycle.
In the following sections, we will delve deeper into the critical mechanisms that underpin system protection and explore the facets of Renesas' end-to-end security offering. This includes robust frameworks for maintaining integrity, privacy, confidentiality, and secure communications, ensuring your product's resilience in an increasingly complex security landscape.
The final section of this post outlines the steps to achieve regulatory compliance and how Renesas can assist.
Main Mechanisms Employed to Protect a System
Renesas ensures security through four critical pillars, each supported by robust mechanisms, detailed examples, and their thorough implementation in our offerings. These mechanisms are supported by hardware (including hardware acceleration) and software provided as part of the Software Development Kit (SDK) for each device.
In this post, we use the DA14535 device (and corresponding 6.0.24 SDK) as an example, but the mechanisms described exist on the majority of the products in the Renesas Connectivity portfolio.
- Authenticity: Renesas Bluetooth Low Energy (LE) devices establish a Root of Trust through unique device identification, true random number generation, and robust encryption. This Root of Trust is the foundation for the security of the entire system. The device boots securely via an immutable bootloader that verifies signed firmware, ensuring that only authenticated updates can be applied. Furthermore, the software development tools (e.g., SDK 6.0.24 for DA14535) include secure firmware update features, leveraging these mechanisms to prevent unauthorized or malicious code execution. This integrated approach helps to ensure the device remains uncompromised from initial deployment to subsequent firmware updates.
- Privacy: The protection of user data is achieved via per-device unique keys, effectively preventing scalable attacks. The DA14535 avoids storing these keys but regenerates them based on non-accessible device information, significantly enhancing data security. SDK 6.0.24 offers APIs that facilitate data encryption and secure storage, enabling developers to implement privacy-centric features efficiently.
- Confidentiality: Intellectual property (IP) is safeguarded through encrypted firmware, which prevents reverse engineering or tampering during deployment. Renesas connectivity devices incorporate encryption protocols, streamlining the secure deployment of proprietary software. Beyond encryption during transfer, the firmware is encrypted while stored and decrypted only when executed, providing an additional layer of protection.
- Secure Communications: Authentication and encryption protocols ensure the confidentiality and integrity of data exchanges. All Renesas Bluetooth Devices support secure communication channels, offering robust APIs, as well as comprehensive examples, to implement encrypted and authenticated data transfer. This mitigates the risks of eavesdropping or man-in-the-middle attacks and unauthorized communication, addressing a critical aspect of device security.
These pillars empower developers to create secure, resilient products that exceed industry standards.
End-to-End Offering
By choosing Renesas, you gain access to tools and resources tailored to secure your product. Our solutions include materials to implement robust security measures while ensuring compliance with standards. Additionally, Renesas provides support across every stage of development, guiding you from initial design to mass production.
A comprehensive strategy for security is needed in every phase of product development, deployment, and usage.
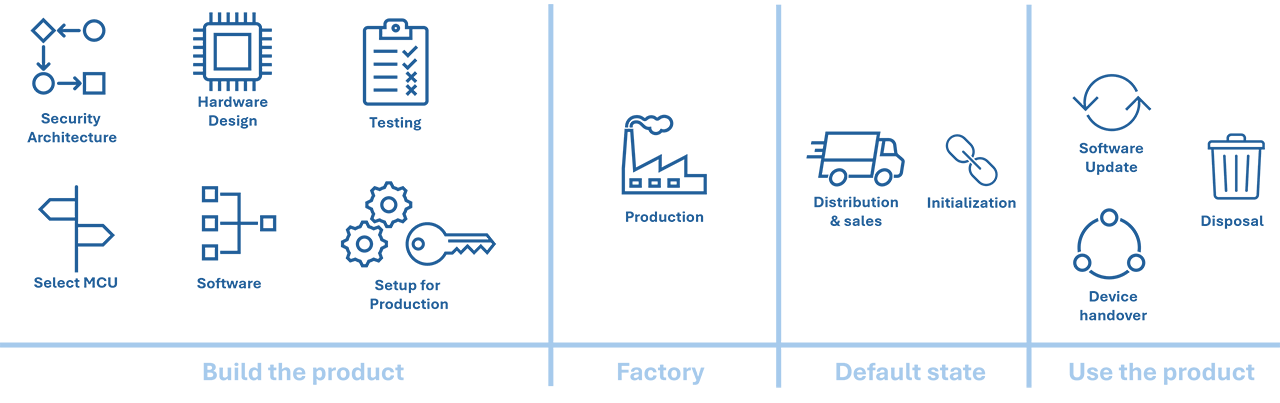
Create Your Product
Start by selecting a radio-enabled device, such as one of Renesas' connectivity products, to build the foundation of secure communication capabilities. The security architecture of your product can give you the parameters for selecting the appropriate device.
Benefit from Renesas' guidance in choosing components that support robust security features, including Bluetooth LE encryption protocols and secure boot mechanisms.
Hardware Design
Renesas provides resources to assist with PCB design, ensuring optimal implementation of security features integrated into hardware layouts.
Guidance on incorporating secure enclosures and tamper-resistant hardware designs to enhance physical security.
Firmware Development
It is tempting to start developing an application and add security to it later. But what is fast now will lead to delays later. Restructuring your code and data, partitioning it so that secure assets are segregated, adding features and mechanisms, are decisions that should be made from the start.
Use Renesas Software Development Kits, such as the 6.0.24, which include APIs for encryption, secure storage, and secure firmware updates.
Testing for Security
Comprehensive testing frameworks provided by Renesas validate firmware, hardware, and communication protocols for vulnerabilities.
Debugging tools ensure that the code executes securely and that the encryption mechanisms function as intended.
Preparation for Production
Assign a dedicated "Security Manager" to oversee the isolation between development and production environments.
Renesas production tools assist in integrating security measures into the production process, including secure programming of assets.
Production
It is crucial to ensure that you do not take risks on the factory floor. When the products are in production, one should not rely on trust in the contract manufacturer or in the workers handling the material and products. Critical assets like the application firmware and the keys that are stored on the device must be handled with security in mind. Renesas provides a complete solution, the Renesas Connectivity Production Line Tool (PLT), that enables testing, trimming, and programming. The PLT is security aware and includes mechanisms to support proper handling of these assets.
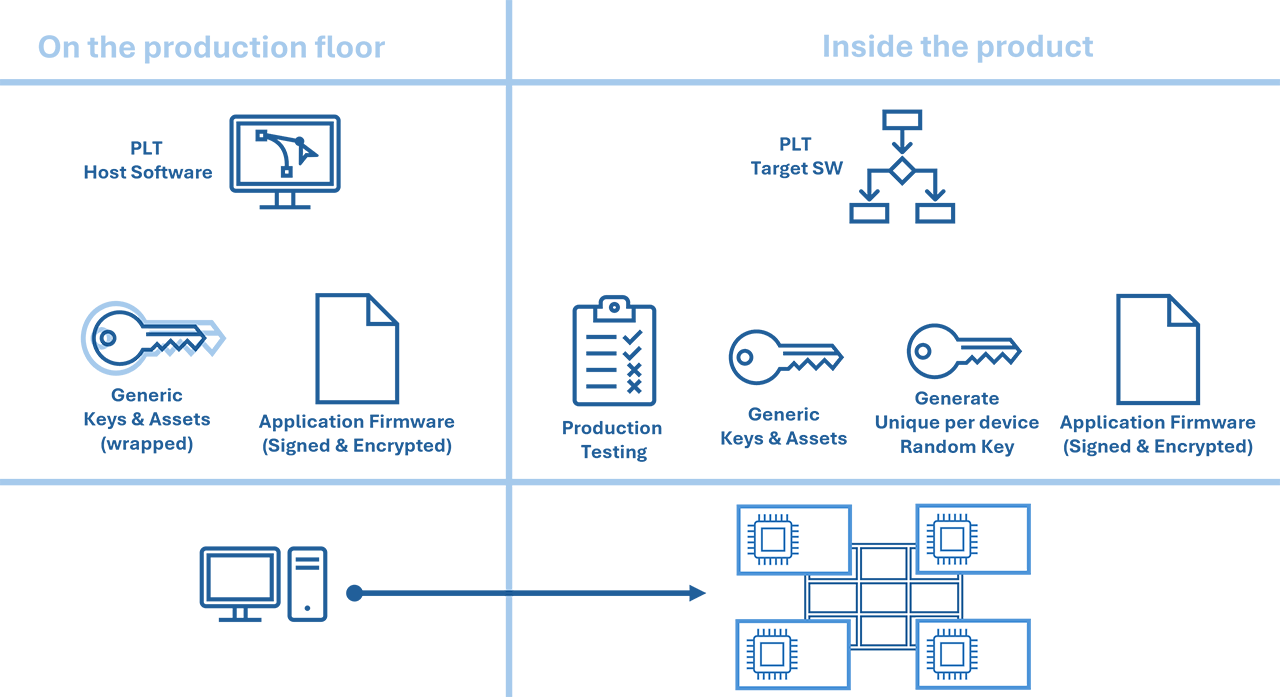
Secure programming of devices using Renesas' PLT ensures that sensitive data and assets are protected.
Product Launch
For market launch, you must comply with relevant regulations. Using Renesas ICs and SDKs will not automatically imply adherence to certification requirements, such as RED, but it is a big stepping stone to ensure that. At Renesas, we test our connectivity products' compliance with the RED Cybersecurity requirements and provide instructions that can be used as a map for your product's CE certification.
Device Initialization
The end user will move the product from the factory default state and configure it so that it can serve its purpose. This initialization links the product with the specific user and makes sure no unauthorized modifications are possible. For example, a Bluetooth product will use secure pairing and bonding and will not allow unbonded users to access any security or personal assets.
Renesas software and hardware integrate industry-standard secure communication protocols, which can be employed to provide such authenticated initialization of the product.
Day-to-Day Usage
During everyday use, the sensitive data or other security parameters of the product are not accessible. Applications can protect private user data with encryption protocols and secure storage mechanisms provided by Renesas SDKs.
It is furthermore recommended to enable monitoring and logging of security events to maintain resilience and detect any irregularities.
Special Use Cases
Apart from day-to-day use, some functions need the authorized user's approval or intervention:
- Transitions, such as device handover to a different user, where all pairing information must be removed and any personal data must be erased.
- Secure software updates to load new features or security hotfixes, without compromising device integrity.
- Product Disposal: Implement mechanisms to ensure secure data removal and device deactivation at the end of its lifecycle.
Regulatory Compliance
An indicative flow to achieve compliance (for example, with the RED Cybersecurity clauses) is shown here:

Build a secure product as explained in the previous sections (make sure all steps are adequately documented)
Check which clause(s) apply to your product. In simple terms:
- If a product is directly or indirectly connected to the internet, then it is in the scope of RED 3.3.d. and must protect the network.
- If a product holds personal data, or is childcare, a toy, or a wearable, then it is in the scope of RED 3.3.e. and must protect personal data.
- If a product is used in monetary transactions, then it is in the scope of RED 3.3.f. and must prevent fraud.
Please check Delegated Regulation (EU) 2022/20, which provides exact guidance.
Choose a method for achieving compliance. Depending on the specifics of your product, the RED Cybersecurity Harmonized Standards (EN 18031-1/2/3) may apply or not (Implementing Decision (EU) 2025/138 documents if and how harmonized standards can be applied). If they apply, you may be able to provide evidence that your product meets these standards, which allows you to self-declare. If they do not apply – or if you cannot prove that your product meets them – you must go through a Notified Body and an independent Test House. Start by preparing your Compliance Dossier.
If you can self-declare based on EN 18031-x:
- Run the conceptual and functional tests and record the results
- Issue a Declaration of Conformity by reference to the Harmonized standards
If you select to go through an external test house and Notified Body:
- Send your product to the test house (with all requested documentation)
- Once tests pass, engage the Notified Body to get a Technical Evaluation Certificate (EU-TEC)
- Issue a Declaration of Conformity by reference to the Notified Body and the applicable standards
Make sure you
- Get experts to support you
- Properly archive all compliance data and evidence
Renesas is enabling you today to launch your products in conformity with active regulations, but is also looking ahead. As security becomes more and more important, and as threats become more elaborate, our products also get updated to be ahead of the curve.
From a regulation perspective, today we provide solutions to comply with RED 3.3d,e,f. Tomorrow, we will enable you to comply with the Cyber Resilience Act (CRA) and other upcoming schemes.
Renesas: Your Trusted Partner
Renesas is a reliable partner looking into the future of cybersecurity. By selecting Renesas connectivity products, you get more than a piece of silicon. You get the hardware, tools, software, and support to enable your compliance journey.
Renesas is committed to providing end-to-end support for implementing security measures. From the first PCB design to mass production and beyond, Renesas experts are there to guide you, ensuring compliance, resilience, and trustworthiness in your product offerings. You can find resources on our product website or contact our customer service directly.
