Forward
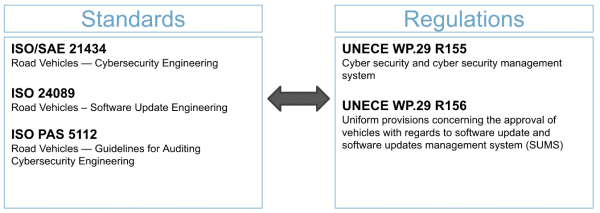
As the automotive industry moves toward full autonomy, the driver relinquishes more responsibilities to the vehicle. This increased scope of control raises the ceiling for software-related recalls as well as potential cyber-risk. As of 2022, software-related recalls issued by the US National Highway Traffic Safety Administration have increased by over 3x from 2009. Additionally, a 2022 Upstream report notes that over 50% of all existing automotive-related Common Vulnerability and Exposures (CVEs) were reported in 2021.
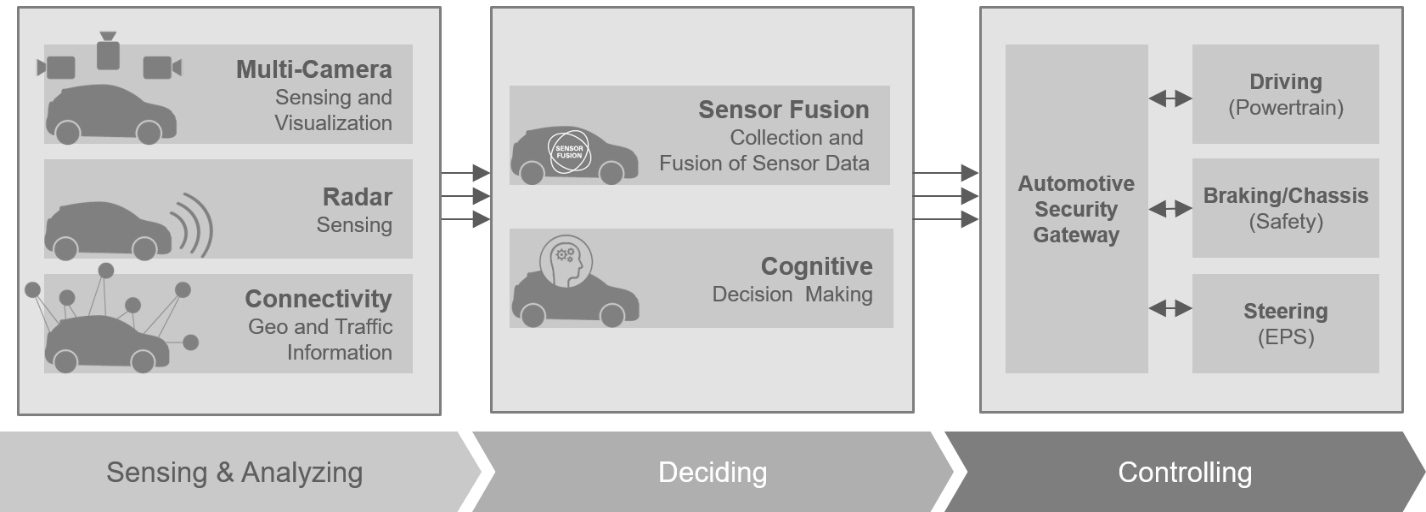
Figure 1: Modern Vehicle Architecture
It is no wonder software updates are an absolute necessity in automotive and, perhaps unsurprisingly, the automotive industry has used software updates in vehicles for many years. Until recently, software updates were generally reserved for development, vehicle manufacturing, or sometimes in a dealership service bay. Vehicles typically received few updates over their lifecycle. On the rare occasion, a software update became available for a vehicle owner, it would typically require a trip to the dealership, or some manual process of updating with USB drives or CD-ROMs/DVDs. This results in an arduous rollout with low uptake. According to NHTSA, over 50% of all software recalls are not yet remedied. In short, the traditional way of doing updates is difficult, burdensome, and inefficient.
This problem space is the main driver of the new ISO 24089 road vehicles standard for software updates engineering as well as the recent UNECE WP.29 R156 regulation on software updates and software management systems. UNECE R156 mandates software update management systems (SUMS) on all new vehicle types by July 2022 and in all new vehicles by 2024. Vehicle manufacturers must now, more than ever, focus on building safe and secure update systems.
Figure 2: Software Update Related Standards and Regulations
Figure 3: Timeline for SUMS
In comes the saviour…
Software over-the-air (SOTA) allows manufacturers to quickly and remotely:
- fix software issues,
- respond to security vulnerabilities,
- and extend or add functionality to a vehicle.
Software issues can be resolved without the need for expensive in-person recalls. Vehicles can be kept up to date with the latest security patches. OEMs (original equipment manufacturers) can add value after the initial sale or open new revenue streams from customers. Conveniently, OEMs can distribute software to an entire fleet at once or roll out updates in stages. All of this can be done from the comfort of an engineer’s ergonomically designed task chair.
Not so fast…the duplicitous nature of software updates
As you might imagine, this update-utopia isn’t entirely as it seems. There is danger hidden beneath the SOTA surface. The same mechanism that brings all these benefits, can also bring destruction. SOTA is by its very nature remote code execution. This tool in the wrong hands can make for a very bad day for an OEM.
Many examples of commercial update systems attacks exist; perhaps the most widely publicized is the SolarWinds exploit. In 2019, attackers compromised the IT management software company SolarWinds’ build system, staying undetected for months. They were able to sign malicious code into the build system to plant remote access tools into the software updates for Orion (SolarWinds’ IT management software). These updates containing malicious backdoors were unwittingly deployed to some 18,000 customers. Major organizations such as Cisco, Microsoft, Intel, and US Government agencies (including the Department of Defence and Department of Homeland Security) were affected. Because the attack was so pervasive and went on for months, the true extent of the damage may never fully be known.
Code signing and secure transport are not enough
The SolarWinds attack perfectly illustrates the problem with many software update systems. Because malicious actors may attack the update system itself, systems that rely on single-key code signing and transport layer security (TLS) may still be open to many types of attacks. Productions update systems must both understand that no system is compromise-proof and work to minimize impact when an attack does happen. By understanding the attacker's goals, designers can work to make systems resilient to attack.
Attackers of update systems intend to:
- Read the contents of updates to discover confidential information, reverse-engineer firmware, or compare two firmware images to highlight changes between versions and perhaps identify vulnerable code sections.
- Deny installation of updates to prevent vehicles from fixing software problems.
- Disrupt functionality in the vehicle, denying use of the vehicle or of certain functions.
- Control ECUs within the vehicle, and possibly the vehicle itself.
- Modify software to execute their own code.
An attacker with access to an update system or signing key may sign malicious updates or deny access to new fixes. If a malicious update is successfully installed in a vehicle, it may be difficult if not impossible to recover without replacing the affected ECU. Therefore, it is important to ensure updates are trusted before installing them.
Backend Security with Uptane
Thankfully, there are experts working to solve these problems. Uptane is a software update security framework specifically designed to meet the diverse needs of automotive software update management systems. Designed by a community of security researchers at NYU, SwRI, and UMTRI, as well as industry leaders in automotive security, Uptane is designed to reduce the effect of known attacks on software update systems, provide resilience against compromise, and minimize the damage if a system does become compromised. Renesas is an active participant in the Uptane standard, partnering with other industry leaders to elevate OTA security.
The Uptane framework takes a pragmatic approach, acknowledging that systems do and will get compromised. By using multiple layers of security and separation of roles, Uptane aims to eliminate single points of failure due to compromise. Uptane minimizes the damage an attacker can do if they obtain a signing key and provides mechanisms for remediation, helping resist against the highest degree of threat actors.
To provide this flexibility, Uptane uses two separate data repositories with different signing authorities. The image repository holds a database of all the signed images an OEM can deploy. Images are signed with offline keys which are themselves signed by a root signing authority. Offline keys are more difficult to compromise remotely because they require physical access and can support added security mechanisms like 2-factor authentication. The director repository takes advantage of the flexibility of online keys for machine-to-machine communication. The director will sign metadata for a particular update campaign instructing the vehicle to install a particular software bundle of software packages. This includes coordinating software updates with multiple ECUs.
Figure 4: Uptane Repository Architecture
Splitting the repositories creates separation of trust. This distributes responsibility so that the compromise of one key doesn’t affect the entire system. Additionally, threshold signatures are supported which can require a minimum number of signatures to attest authenticity of updates, again reducing the impact of a single key compromise. Revocation and updating of keys are an integral part of Uptane, providing a mechanism for replacing a compromised key. The most impactful keys, such as root keys and image signing keys, are designed to be offline. This minimizes the attack surface for the highest impact and most privileged keys.
Figure 5: Uptane Ecosystem
Renesas Device Security
Along with participation in the Uptane standard, Renesas is working to secure the entire end-to-end software update chain of trust. While Uptane allows an ECU to determine the authenticity and providence of software updates, several fundamental security attributes are needed including:
- ECUs must have reasonable assurance that the updated software itself is trusted and unaltered
- ECUs must have mechanisms to authenticate updates
- ECUs must have mechanisms to securely store critical keys used in the update process
- ECUs must have mechanisms to detect software tampering after an update is accepted
For these reasons, on-device security is imperative, and Renesas automotive devices supply the tools needed to increase security, lower the risk of compromise, and ensure software validity and authenticity.
After the software is validated and installed, it is up to the device to ensure the software is not tampered with after installation. This is where the secure boot is needed, and Renesas automotive devices support secure boot using dedicated security hardware, helping ensure ECU software stays trusted through the device lifecycle. Our recent blog series on secure boot in Renesas automotive devices goes into greater details on these foundational concepts.
In addition to facilitating secure boot, the ICU-M (intelligent cryptographic unit master) hardware protected security environment in R-Car and RH850 devices enables secure storage of cryptographic key material and other critical data. Secure key storage is essential to the security of the overall update system. A more in-depth breakdown of security features is found on our Renesas Secure – Automotive home page.
Renesas automotive devices also include dedicated hardware cryptographic accelerators. These can be used to accelerate secure communication such as TLS, as well as generate high entropy random numbers for nonces and challenge/response protocols.
Conclusion
As the industry pushes to implement the latest updates related standards and regulations, we must ensure the continued safety and security of automotive vehicle systems. OTA is a double-edged sword. It is both a mechanism to facilitate a wealth of features and security updates and a significant attack vector for adversaries. Renesas actively contributes to the Uptane standard development and builds security enablement mechanisms directly into our automotive devices, increasing the resilience of update systems in the face of compromise. Renesas automotive devices incorporate security measures including:
- Hardware protected security environments for storing keys and running security firmware,
- Secure boot to ensure software is authentic and unmodified, and
- Cryptographic accelerators for speeding up signature checks and secure communication.
Secure software update management systems combined with on-devices security ensure the best solution against attacks. Renesas continues to be a leading partner in secure software update innovation.